The EFI Shell is a 'shell' (think of a command prompt or a terminal shell) that a (U)EFI 'BIOS' can directly boot into (instead of your OS) allowing control and scripting of many items including booting scenarios. Step 3: Using your CB Quick Tune EFI Software A) A profile was programmed into your EMS by a CB EFI Tech before shipment of your kit. Profile settings do not affect the content of the profile. Fiery Command WorkStation. Hide or show navigation Previous topic Next topic Share Print PDF. Edit profile settings. Profile settings are attributes that determine how the Fiery server uses the profile. For example, you can assign a description or media type to a profile.
Fiery color management
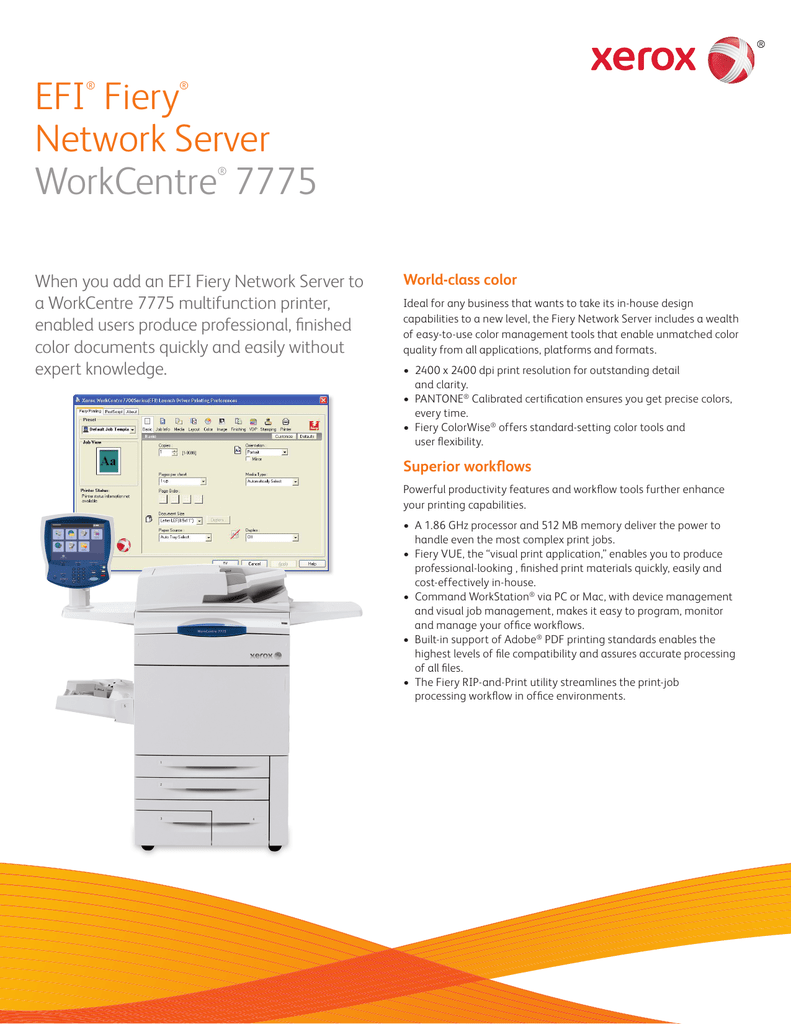
Fiery® color management tools give you maximum control over color quality. ICC-based color management technology is integrated in every Fiery server and works directly with advanced controls in Fiery Command WorkStation®. Fiery Color Profiler Suite is integrated with the Fiery server to create best-in-class ICC output profiles for each substrate in a few simple steps.
Excellent out-of-the-box color
Fiery servers deliver professional color quality right out of the box. Easy-to-use tools ensure the accuracy and consistency every printing business requires. The latest Fiery digital front ends benefit from EFI's next-generation color profiling technology Fiery Edge™ which further enhances out-of-the-box results.

Efi Profile Editor
Dependable color accuracy- Achieve the best match for logo and brand colors
- Shorten turnaround times by printing on multiple print engines capable of producing the same output
- Reduce job rejections with reliable reproduction of complex, graphically-rich content files
- Produce color to a specified standard at all times
All the tools you need to get your color right – Fiery Color Profiler Suite
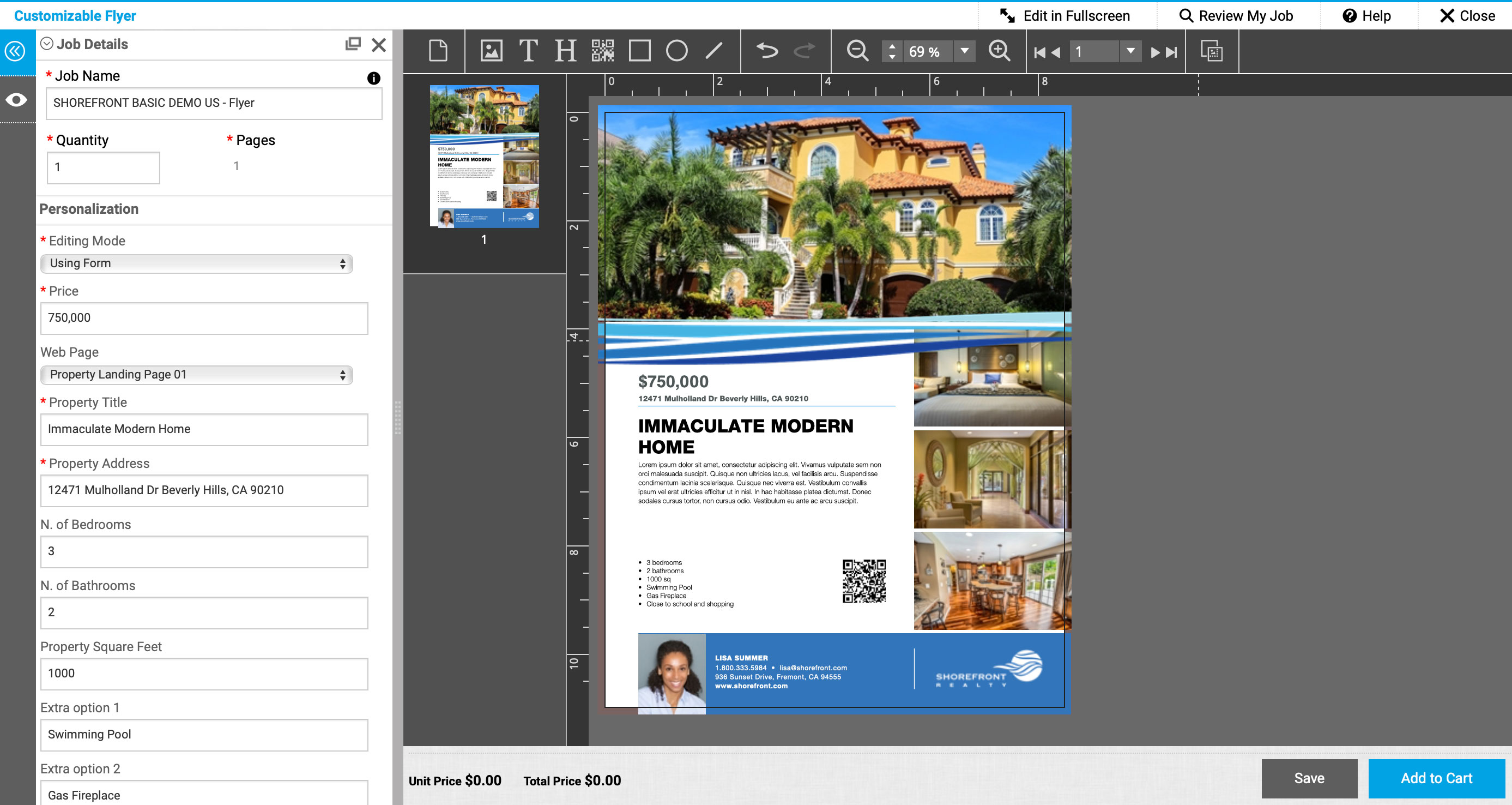
Fiery Color Profiler Suite offers a comprehensive set of market-leading color management tools that provide integrated color quality control at every stage of the printing workflow. Creating custom profiles using this technology ensures color reproduction is always accurate, consistent and reliable. It is the only profiling toolset on the market to integrate directly with both toner and inkjet Fiery servers. This seamless integration enables even a novice user to succeed at profiling a printer and paper combination, and then verifying the precision of color matching in just a few quick steps. It is also tightly integrated with Fiery Command WorkStation features such as Calibrator, Spot-On™ and Fiery ImageViewer. For users of the latest Fiery digital front ends, Fiery Edge profiling technology offers further user controls with Color Profiler Suite to enhance output such as boosting color saturation, and advanced black controls.
EFI offers a selection of spectrophotometers to precisely measure color with Fiery Color Profiler Suite in order to match industry color standards such as ISO, FOGRA and GRACoL (G7).
Bcd Editor Efi
Fiery imaging technology
Fiery servers give you the highest level of performance and image quality, even on complex jobs with gradients, transparencies or overprints — even in VDP elements. The controls in Fiery Command WorkStation Job Properties provide complete access to all Fiery imaging features to ensure jobs print as the print buyer expects.
Exceptional image quality- Automatic correction of potential mis-registration
- Smooth low-resolution images
- Sharpen and smooth black text and line art and minimize jaggies
- Eliminate “stair stepping” gradient shades in vector images
- Reproduce overprinted elements correctly
Easy image adjustments with Fiery Image Enhance Visual Editor
- On-the-fly correction for individual images without modifying design files
- Manual controls also allow visual adjustment for:
- Brightness
- Contrast
- Highlights
- Shadows
- Color balance and skin tones
- Sharpness
- Red-eye
Secure boot is a security standard developed by members of the PC industry to help make sure that a device boots using only software that is trusted by the Original Equipment Manufacturer (OEM). When the PC starts, the firmware checks the signature of each piece of boot software, including UEFI firmware drivers (also known as Option ROMs), EFI applications, and the operating system. If the signatures are valid, the PC boots, and the firmware gives control to the operating system.
The OEM can use instructions from the firmware manufacturer to create Secure boot keys and to store them in the PC firmware. When you add UEFI drivers, you'll also need to make sure these are signed and included in the Secure Boot database.
For information on how the secure boot process works included Trusted Boot and Measured Boot, see Secure the Windows 10 boot process.
Secure boot requirements

In order to support Secure boot, you must provide the following.
| Hardware requirement | Details |
|---|---|
| UEFI Version 2.3.1 Errata C variables | Variables must be set to SecureBoot=1 and SetupMode=0 with a signature database (EFI_IMAGE_SECURITY_DATABASE) necessary to boot the machine securely pre-provisioned, and including a PK that is set in a valid KEK database. For more information, search for the System.Fundamentals.Firmware.UEFISecureBoot system requirements in PDF download of the Windows Hardware Compatibility Program Specifications and Policies. |
| UEFI v2.3.1 Section 27 | The platform must expose an interface that adheres to the profile of UEFI v2.3.1 Section 27. |
| UEFI signature database | The platform must come provisioned with the correct keys in the UEFI Signature database (db) to allow Windows to boot. It must also support secure authenticated updates to the databases. Storage of secure variables must be isolated from the running operating system such that they cannot be modified without detection. |
| Firmware signing | All firmware components must be signed using at least RSA-2048 with SHA-256. |
| Boot manager | When power is turned on, the system must start executing code in the firmware and use public key cryptography as per algorithm policy to verify the signatures of all images in the boot sequence, up to and including the Windows Boot Manager. |
| Rollback protection | The system must protect against rollback of firmware to older versions. |
| EFI_HASH_PROTOCOL | The platform provides the EFI_HASH_PROTOCOL (per UEFI v2.3.1) for offloading cryptographic hash operations and the EFI_RNG_PROTOCOL (Microsoft defined) for accessing platform entropy. |
Signature Databases and Keys
Before the PC is deployed, you as the OEM store the Secure Boot databases on the PC. This includes the signature database (db), revoked signatures database (dbx), and Key Enrollment Key database (KEK). These databases are stored on the firmware nonvolatile RAM (NV-RAM) at manufacturing time.
The signature database (db) and the revoked signatures database (dbx) list the signers or image hashes of UEFI applications, operating system loaders (such as the Microsoft Operating System Loader, or Boot Manager), and UEFI drivers that can be loaded on the device. The revoked list contains items that are no longer trusted and may not be loaded. If an image hash is in both databases, the revoked signatures database (dbx) takes precedent.
The Key Enrollment Key database (KEK) is a separate database of signing keys that can be used to update the signature database and revoked signatures database. Microsoft requires a specified key to be included in the KEK database so that in the future Microsoft can add new operating systems to the signature database or add known bad images to the revoked signatures database.
After these databases have been added, and after final firmware validation and testing, the OEM locks the firmware from editing, except for updates that are signed with the correct key or updates by a physically present user who is using firmware menus, and then generates a platform key (PK). The PK can be used to sign updates to the KEK or to turn off Secure Boot.
You should contact your firmware manufacturer for tools and assistance in creating these databases.
Efi Profile Editor Free
Boot sequence
- After the PC is turned on, the signature databases are each checked against the platform key.
- If the firmware is not trusted, the UEFI firmware must initiate OEM-specific recovery to restore trusted firmware.
- If there is a problem with Windows Boot Manager, the firmware will attempt to boot a backup copy of Windows Boot Manager. If this also fails, the firmware must initiate OEM-specific remediation.
- After Windows Boot Manager has started running, if there is a problem with the drivers or NTOS kernel, Windows Recovery Environment (Windows RE) is loaded so that these drivers or the kernel image can be recovered.
- Windows loads antimalware software.
- Windows loads other kernel drivers and initializes the user mode processes.